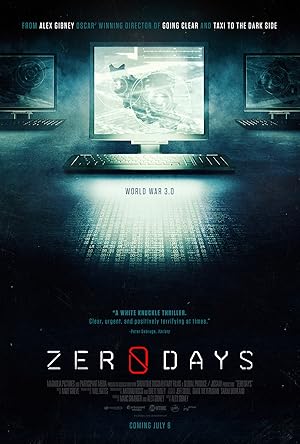
Zero Days Page #2
Activists, or hacktivists,
they are hacking for fun
or hacking to push
some political message.
And the third group
is nation-states.
They're interested in
high-quality intelligence
or sabotage activity.
Chien:
Security companiesnot only share information
but we also share
binary samples.
So when
this threat was found
by a Belarusian
security company
on one of their customer's
machines in Iran,
the security community.
When we try to name threats,
we just try to pick
some sort of string,
some sort of words,
that are inside
of the binary.
In this case, there was
and we took pieces of each,
and that formed stuxnet.
I got the news about stuxnet
from one of my engineers.
He came to my office,
opened the door,
and he said, "so, Eugene,
of course you know that
we are waiting
It happened."
Gibney:
Give me somesense of what it was like
in the lab at that time.
Was there a palpable
sense of amazement
that you had something
really different there?
Well, I wouldn't call it
amazement.
It was a kind of a shock.
It went beyond our worst fears,
our worst nightmares,
and this continued
the more we analyzed.
The more we researched,
the more bizarre
We look at so much malware
every day that
we can just look at the code
and straightaway we can say,
"okay, there's something bad
going on here,
and I need to
investigate that."
And that's the way it was
when we looked at stuxnet
for the first time.
just bad things everywhere.
Just like, okay, this is bad
and that's bad,
and, you know,
we need to investigate this.
And just suddenly
we had, like,
a hundred questions
straightaway.
The most interesting thing
that we do is detective work
where we try to track down
who's behind a threat,
what are they doing,
what's their motivation,
and try to really stop it
at the root.
And it is kind of
all-consuming.
You get this new puzzle
and it's very difficult
to put it down,
you know, work until, like,
4:
00 am in the morningAnd I was in that zone where
I was very consumed by this,
very interested to know
what was happening.
And Eric was also
in that same sort of zone.
So the two of us were, like,
back and forth all the time.
Chien:
Liam and I continuedto grind at the code,
sharing pieces,
comparing notes,
bouncing ideas
off of each other.
We realized that
we needed to do
what we called deep analysis,
pick apart the threat,
every single byte,
every single zero, one,
Translation
Translate and read this script in other languages:
Select another language:
- - Select -
- 简体中文 (Chinese - Simplified)
- 繁體中文 (Chinese - Traditional)
- Español (Spanish)
- Esperanto (Esperanto)
- 日本語 (Japanese)
- Português (Portuguese)
- Deutsch (German)
- العربية (Arabic)
- Français (French)
- Русский (Russian)
- ಕನ್ನಡ (Kannada)
- 한국어 (Korean)
- עברית (Hebrew)
- Gaeilge (Irish)
- Українська (Ukrainian)
- اردو (Urdu)
- Magyar (Hungarian)
- मानक हिन्दी (Hindi)
- Indonesia (Indonesian)
- Italiano (Italian)
- தமிழ் (Tamil)
- Türkçe (Turkish)
- తెలుగు (Telugu)
- ภาษาไทย (Thai)
- Tiếng Việt (Vietnamese)
- Čeština (Czech)
- Polski (Polish)
- Bahasa Indonesia (Indonesian)
- Românește (Romanian)
- Nederlands (Dutch)
- Ελληνικά (Greek)
- Latinum (Latin)
- Svenska (Swedish)
- Dansk (Danish)
- Suomi (Finnish)
- فارسی (Persian)
- ייִדיש (Yiddish)
- հայերեն (Armenian)
- Norsk (Norwegian)
- English (English)
Citation
Use the citation below to add this screenplay to your bibliography:
Style:MLAChicagoAPA
"Zero Days" Scripts.com. STANDS4 LLC, 2024. Web. 25 Apr. 2024. <https://www.scripts.com/script/zero_days_23977>.


Discuss this script with the community:
Report Comment
We're doing our best to make sure our content is useful, accurate and safe.
If by any chance you spot an inappropriate comment while navigating through our website please use this form to let us know, and we'll take care of it shortly.
Attachment
You need to be logged in to favorite.
Log In